You need a written self-custody procedure to securely manage your digital assets and avoid costly mistakes. It provides clear steps, helps keep your security measures consistent, and reduces risks like loss or theft. Documenting your process ensures you don’t forget critical tasks and stays organized as your assets grow. Having a plan also makes it easier to adapt your security practices over time. Keep going to discover how you can create an effective self-custody system.
Key Takeaways
- Ensures consistent and correct management of private keys, reducing human errors.
- Provides a clear security roadmap to protect assets from theft or loss.
- Facilitates regular updates and reviews to adapt to evolving threats.
- Supports compliance and accountability through documented procedures.
- Enables effective training and knowledge transfer for responsible asset management.

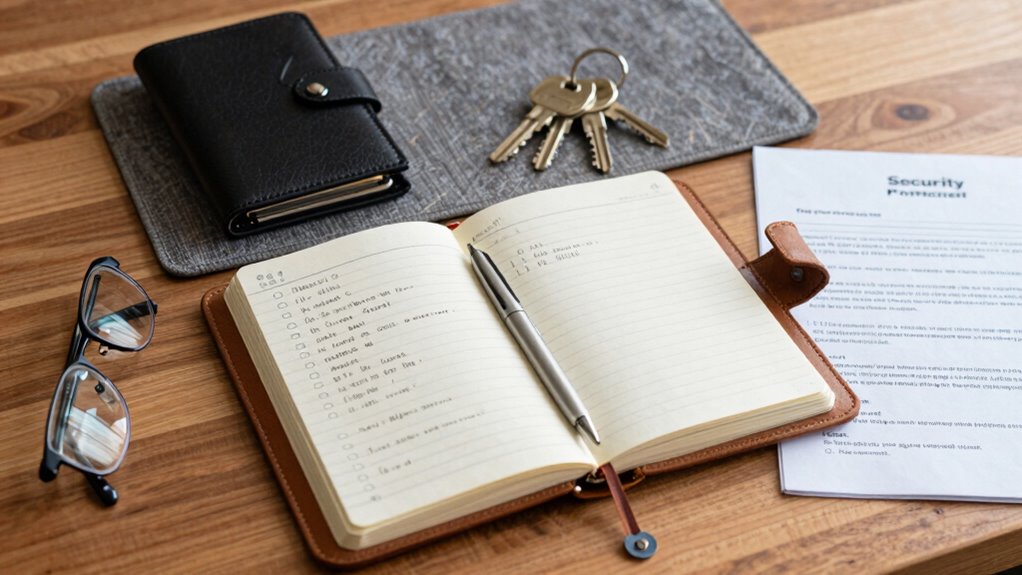
Are you wondering how to securely manage your digital assets? Self-custody offers control and independence, but it also comes with significant responsibilities. To keep your assets safe, you need a clear, written procedure. Without a documented plan, it’s easy to make mistakes that could compromise your digital security and violate compliance standards. A well-crafted procedure acts as your roadmap, ensuring each step is performed consistently and correctly, reducing risks of loss or theft.
A clear, written procedure is essential for secure, consistent self-custody of digital assets.
When you handle your digital assets independently, you’re solely responsible for their security. Digital security isn’t just about using strong passwords or enabling two-factor authentication; it requires an all-encompassing strategy that covers everything from secure storage to backup protocols. A written procedure helps you define these measures explicitly, ensuring you don’t overlook critical steps. You might think, “I know what I’m doing,” but over time, routine tasks can become blurry or forgotten. Documenting your process keeps your approach disciplined and reduces the chance of errors.
Additionally, understanding the importance of contrast ratio and how it impacts image clarity can be a useful analogy for recognizing the significance of contrast in security protocols. Having a written procedure fosters consistency, especially if you manage multiple assets or share responsibilities with others. It minimizes the risk of human error, such as misplacing private keys or mishandling recovery procedures. When you follow a documented process, you create a reliable system that can be easily reviewed or improved over time. Incorporating standard operating procedures ensures that your security practices are comprehensive and repeatable, further strengthening your safeguards. Regularly reviewing and updating your protocols can also help address emerging security threats and technological changes, making your security measures more resilient.
This documentation also acts as a training tool if someone else needs to step in temporarily, ensuring they follow the correct security protocols without guesswork. In essence, self-custody isn’t just about holding your assets; it’s about actively maintaining their safety. A written procedure makes this task manageable and scalable. It aligns your practices with digital security best practices and compliance standards, giving you peace of mind that your assets are protected and your procedures are transparent. Without it, you’re leaving your assets vulnerable to human error and regulatory pitfalls, making a clear, documented process an essential part of responsible self-custody. Incorporating clear documentation ensures that your security measures are both effective and adaptable to future changes. Additionally, implementing regular audits can help verify that your procedures are being followed correctly and remain effective against evolving threats.

Trezor Safe 3 – Passphrase & Secure Element Protected Crypto Hardware Wallet – Buy, Store, Manage Digital Assets Simply and Safely (Cosmic Black)
Unparalleled Security: Protect your assets NDA-free EAL 6+ Secure Element, offering robust defense and complete transparency
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Often Should I Review My Self-Custody Procedures?
You should review your self-custody procedures at least quarterly to stay ahead of potential risks and guarantee effective contingency planning. Regular reviews help identify new vulnerabilities, adapt to changing circumstances, and refine your risk assessment. If you experience significant changes in your holdings or security environment, update your procedures immediately. Consistent reviews keep your self-custody approach robust, minimizing risks and ensuring your assets remain protected under evolving conditions.
What Tools Are Best for Secure Record-Keeping?
Did you know that 60% of data breaches involve weak record-keeping? For secure record-keeping, you should use tools that prioritize digital encryption to protect your information. Consider hardware wallets or encrypted digital vaults for storing keys, and implement robust backup strategies to prevent data loss. These tools guarantee your records stay confidential and accessible only to you, maintaining the integrity of your self-custody setup.
How Do I Update My Procedures After a Security Breach?
After a security breach, you should update your procedures by reviewing and strengthening your emergency protocols to address vulnerabilities. Conduct thorough staff training to guarantee everyone understands new security measures and response steps. Document these updates clearly in your written procedures, and regularly test them through drills. This proactive approach helps prevent future breaches and keeps your self-custody system resilient and secure.
Who Should Have Access to My Self-Custody Records?
You should limit access to your self-custody records to trusted individuals who need it for their roles, implementing strict access control measures. Keep records transparent within your trusted team while protecting sensitive information from unauthorized eyes. Regularly review and update access permissions to make certain only authorized personnel can view or modify records. This approach helps maintain security, accountability, and integrity of your self-custody holdings.
What Are Common Mistakes to Avoid in Self-Custody?
Did you know that nearly 70% of self-custody losses are due to procedural mistakes? To prevent this, prioritize custody oversight and keep detailed procedural documentation. Common mistakes include neglecting regular security reviews, failing to update access controls, and not documenting all procedures properly. You need clear, written procedures to guarantee consistent practices, reduce human error, and safeguard your assets effectively. Don’t overlook the importance of thorough documentation in self-custody.

SAMYERLEN Crypto Seed Phrase Storage, 304 Stainless Steel Secure Bitcoin Wallet, Private Key Recovery Cold Storage Backup 3 Plates 24 Words Compatible with BIP39 Hardware Wallets, Ledger, Trezor
Safeguard Your Crypto Assets: The SAMYERLEN Tablet is made of grade 304 steel and features intense laser engraving,…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Having a written self-custody procedure is like having a map in uncharted territory—you know exactly where to go and what to do. It keeps your assets safe, organized, and accessible when you need them most. Without it, you’re like a sailor lost at sea, vulnerable to storms and confusion. So, document your steps clearly; it’s your best compass to secure and manage your digital valuables confidently.

Thousands of Images, Now What: Painlessly Organize, Save, and Back Up Your Digital Photos
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Crypto Seed Cold Storage Wallet with Engraver Pen Kit – Metal Plate and Etching Tool for Cryptocurrency Password Phrase Backup and Recovery
All Inclusive Kit for Crypto Seed Key Storage – Comes a Stainless Steel Plate & Tungsten Steel Engraving…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.